One of the most important parts of cybersecurity is actually having a backup and disaster recovery plan in place. This is often the area that many practices overlook because it may involve someone needing to be involved and this makes it easier to be forgotten. But what’s worse than thinking you have a good disaster plan in place? Having one that doesn’t actually protect your business at all. This is what happened to Apex HCM earlier this year. Ransomware managed to make its way onto their network and their backup and disaster recovery system wasn’t able to help them. Find out what happened and what you need to do to ensure your own practice of business is secured.
What happened?
On February 19th, Roswell, Georgia based Apex HCH was infected with ransomware. Apex HCH is a cloud-based payroll company that provides services to payroll service companies, who in turn, provide services to small and mid-sized businesses. The ransomware encrypted all of the data on their main systems incredibly fast. It then demanded payment to provide the company with a key to unlock their data.
At this point, most companies would resort to their backup and disaster recovery plan to help restore the data and operations. The company pulled all the infected servers offline and started the process of notifying its customers of the breach. According to Brian Krebs, a security author, the ransomware never touched the customers of Apex HCH’s data. Instead, it infected all of the internal systems of the company and this made it impossible to run operations. Krebs reached out to Apex and spoke with Ian Oxman who is the company’s chief marketing officer. Oxman had this to say:
“We had just recently completed a pretty state-of-the-art disaster recovery plan off-site out and out of state that was mirroring our live system,” Oxman said. “But when the ransomware bomb went off, not only did it go through and infect our own network, it was then immediately picked up in our disaster recovery site, which made switching over to that site unusable.”
Let that sink in for a moment. The company thought they had just implemented a thorough, state of the art, backup, and disaster recovery plan. They thought that they had this all covered. But due to poor implementation, the system didn’t work. After several days of trying to restore the data, at the advisement of computer security firms, Apex HCH paid the ransom.
Paying ransom didn’t solve the issue
However, even paying the ransom didn’t solve the problem. The ransomware didn’t restore the data in its original state. Some of the programs that were infected were rendered unusable even after decryption. This, in turn, delayed the restoration process.
The company did not disclose how much was paid as ransom.
It should be of concern to business owners that even paying a ransom may not get them back up and running. Many companies don’t have a backup or disaster recovery plan in place. So when they do get infected with ransomware, the only option is to pay. However, if that won’t deliver the promised result of restoring the business, then the business is out of options. That is why having a good backup disaster recovery plan is so crucial for any business, but especially so for small businesses who often lack the resources of larger businesses.
What is a backup disaster recovery plan?
A backup disaster recovery (also called BDR) plan is the documented process a company will follow should they need to restore their data operations in the event that data becomes unusable. Most people think of this as happening when a hacker attacks a company, however, another need for BDR is in natural disasters or robbery. If you arrived at your office to find that all the computers had been stolen, would you be able to restore and be back up and running? How long would it take?
Our data has now become too important to how our businesses run to be handled without proper backups in place.
3..2..1.. ready for reliable backup disaster recovery plan?
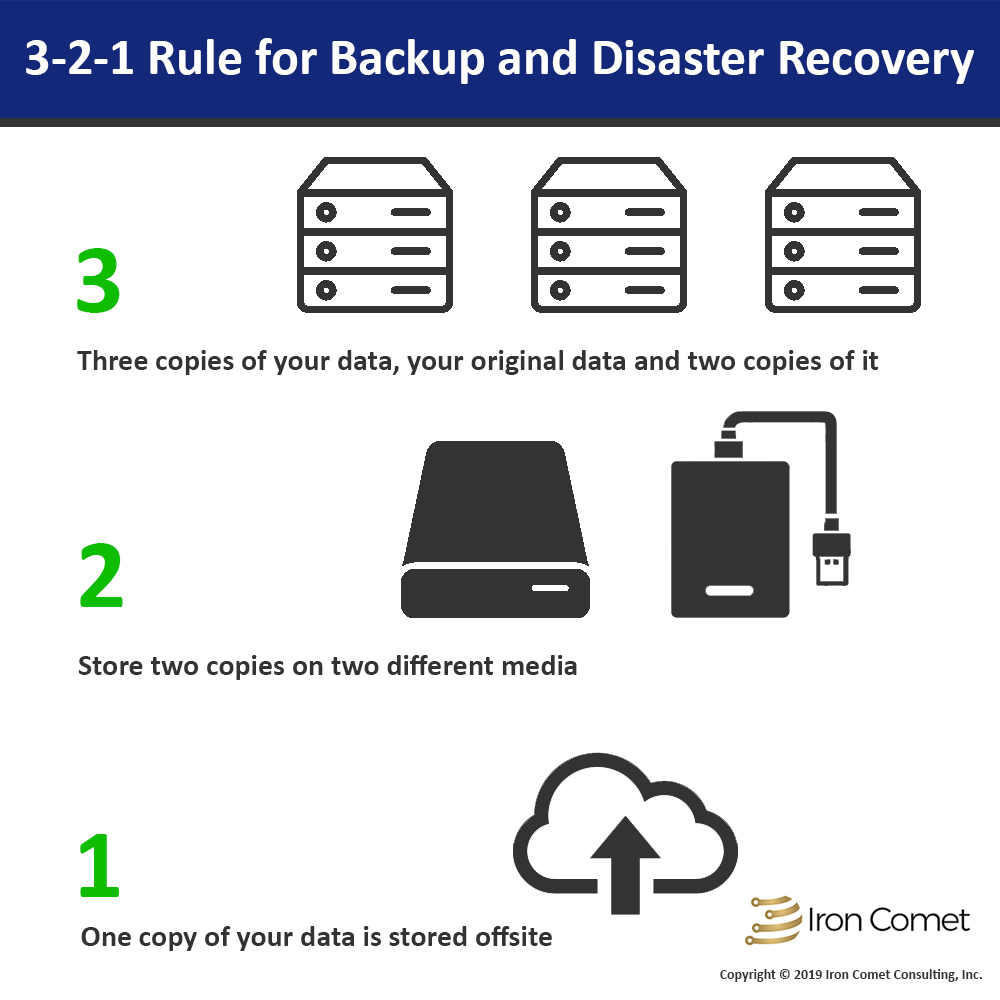
The most reliable way to protect your business’ data is to use the 3 2 1 system for backups. This means:
- 3 separate backups of the data
- 2 different types of backups (two different mediums)
- 1 backup offsite
This system protects your data from many different forms of attacks but also in the event of a natural disaster of robbery.
OK, so how would this work in your business?
Your main data is stored on the server in your office. That is your original data. From there, you would have an external hard drive that is plugged into the server. It backups up at a specific time each day, not in real time. At the end of the day, these drives are swapped and one is taken offsite.
3 – We have the original data and 2 additional copies
2 – The data is on the server and external hard drives (2 different media)
1 – One of the drives is always offsite
Using a cloud service would be an alternative to swapping external drives daily. The amount of data would be the determining factor of if this was a realistic option for your business.
You can make changes to this basic system to fit your own needs. For example, you can swap a network attached storage for the external drive and then upload it from there to the cloud.
Final Thoughts
For most small businesses, you won’t need real-time backup. This is important for those businesses that don’t have a dedicated IT person on staff to make sure that ransomware doesn’t make it to the backups. Ideally, you would want to have one backup that is not connected anywhere at any time. For example, the external drive that is offsite and not connected to any computer. If you were infected with ransomware, that backup would not be impacted. A cloud backup could become infected if the ransomware isn’t noticed and the infected data is copied to the cloud, overwriting your good data.
Protecting our data is becoming harder for the nature of the threats we all face. Ransomware attacks have increased dramatically since they were first discovered. By implementing a multi-level approach to protecting your data, like the 3-2-1 system, you will prevent these issues from happening.
[DISPLAY_ULTIMATE_SOCIAL_ICONS]
