In the technology field, it’s inevitable that older devices get replaced. With Windows 7 reaching its end of life in January 2020, many practices will be doing just that. But a new study released by Blancco Technology Group showed that an alarming number of used hard drives being offered for sale online still contain sensitive data. For a medical practice, this could turn into a HIPAA nightmare, should these drives contain protected health information (PHI).
Blancco Technology Group and data recovery company Ontrack performed a study where they purchased 159 used hard drives from sellers in the United States, the United Kingdom, Finland, and Germany. The drives were purchased at random and included well-known brands such as Dell, Seagate, Samsung, Hitachi, and HP. One interesting part of the study was that Blannco asked each of the sellers if they had properly disposed of the data on the drives. Each seller stated that they had erased everything from each drive before selling.
Once the used hard drives were received, OnTrack used its data recovery software on each of the drives and was able to recover sensitive data on 42% of the drives. To make matters worse, more than 15% of the drives contained personally identifiable information including emails, photos, Microsoft Word and Excel documents, and other personal files.
According to the study, one drive, in particular, stood out from the others. It belonged to a software developer who had been given a government security clearance. The drive was found to contain scanned copies of his family’s passports, birth certificates, and financial information.
Blannco conducted a similar study in 2016 that yielded similar results. In that study, the company purchased 200 drives from eBay and Craigslist. Their tests revealed that 67 percent of them contained information that was personally identifiable.
Why do these used hard drives still contain data?
Blannco said that every person or company they purchased from insisted that the drives were properly wiped, or erased before purchase. They were assured that the drives contained no data. What often happens is that sellers only use the format option to erase the drives. Formatting a drive simply removes the index, a table of contents of sorts, for the files on the drive. It doesn’t actually destroy the data. Anyone that bought the device could run undelete or data recovery tools on it and the data would be accessible.
One thing that should be noted from this study is that many companies cannot be trusted to thoroughly destroy the data contained on these devices. Each stated that all data had been thoroughly erased but as we can see, this was not the case. Trusting an unknown third party with PHI is a gamble on your part.
What is the best way to sanitize your old hard disks?
For medical practices, you must properly destroy the data on any hard disk that you are no longer using. The main consideration is whether or not the drive should be sold or given away. If it was used in a server and contained a large amount of PHI, its best to destroy the device rather than recycling it.
Drives can be destroyed in a variety of means. The easiest is to use a power drill and drill 4 holes through the platters of the device. This will render it unusable.
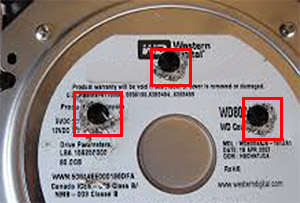
hard drive with 3 holes drilled in it
The second option is to use a service that will destroy the drives for you. Services usually do this one of two ways. They will use devices that destroy all of the data on the drives themselves or they will be recycled into scrap metal. The second option is the most secure.
If you choose to use a service, be sure to get a certificate of destruction to add to your HIPAA documentation for each drive you send to the service. This is critical as it serves as proof that you performed your due diligence to destroy any data. If any of these drives end up in public and someone posts the data that was found, you will have a far easier time if you can prove you did your part.
If you have decided that you do wish to resell or gift the hard drives (by giving away the computer itself), then perform a software destruction of the drives.
One tool that is easy to use is DBAN (Darik’s Boot and Nuke). DBAN creates a bootable CD or USB flash drive. It will boot the computer into its software where you can select what method of destruction you would like to use. DBAN was sold to Blannco but the original is still available at the link above.
DBAN will not work on SSD drives. If your computer has a newer SSD type drive, then you will need a different tool.
For SSD drives, you can use Secure Erase Utility made available by the University of California – San Diego.
Before you donate or sell your old computers, make sure all of the data they contain has been securely deleted. Don’t end up on HIPAA’s Wall of Shame for a mistake that is entirely avoidable.
[DISPLAY_ULTIMATE_SOCIAL_ICONS]